Back in 2012, GDS released some security guidelines for government services. Although we’re aware individual services have continually upgraded their own security practices, we’re now updating the guidelines to improve how we secure government services overall.
We’ll be making 2 important updates to the guidelines that will take effect from 1 October 2016. If you run a service on service.gov.uk, you’ll need to be aware of these.
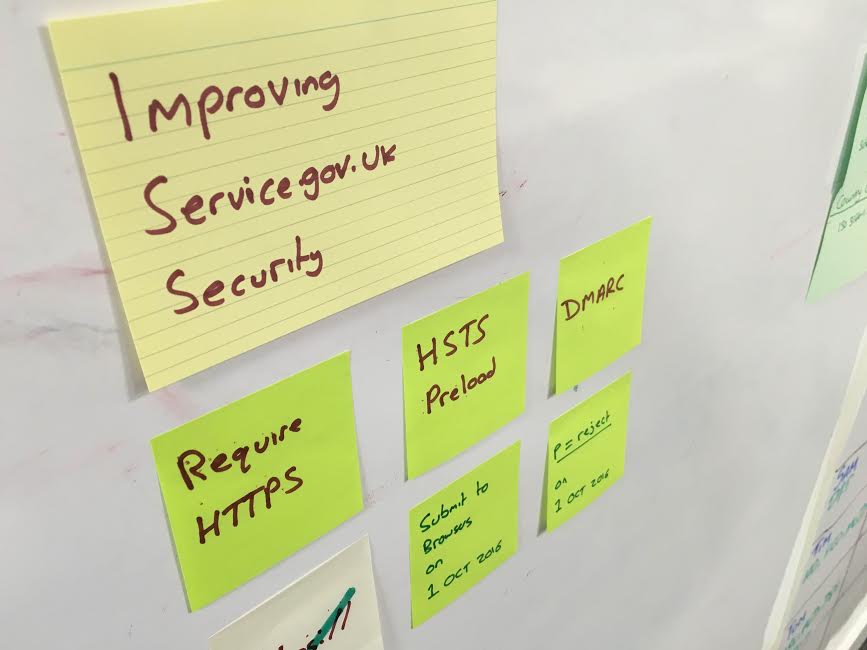
What is changing
From the beginning of October, your service will need to make sure it:
- runs on secure HTTPS connections and uses HSTS
- has published a Domain-based Message Authentication, Reporting & Conformance (DMARC) policy
If you’re a service manager, you’ll need to speak with your technical team to make sure your service is fully compliant by the October deadline.
Ensuring secure connections
The service.gov.uk standards require all government services to run on secure connections, known as ‘HTTPS’. This type of connection makes sure user data is encrypted and stays secure while users interact with your service.
As well as enforcing the use of HTTPS, we now mandate that service uses HTTP Strict Transport Security (HSTS). This setting tells modern browsers your service will only use secure connections and information should be sent encrypted.
In September, we plan to submit the service.gov.uk domain to the browser manufacturers’ HSTS preload list. This means that all modern browsers will only ever connect to government services via HTTPS. If you service is only available over unsecured connections, it will stop working in modern browsers once this happens. This may also affect testing environments hosted on service.gov.uk.
Publishing a DMARC policy
Government Digital Service has published guidance on how to implement secure email practices including Domain-based Message Authentication, Reporting and Conformance policies, known as DMARC. Such policies ensure your domain cannot be used by email phishers and scammers.
Services should publish a DMARC policy and set it to the highest level, called ‘p=reject’. If you have not set up this policy by 1 October 2016, your emails may be rejected by external email providers.
As a temporary measure, if your team cannot set the DMARC policy to p=reject in this time period, you should should publish a record using ‘p=none’ to override the default policy.
These updates are aimed at maintaining secure services and trust in digital government services. In relation to this, we’ll soon be publishing new security content in the Service Manual to help service teams pass the Service Standard. Stay tuned!
You can follow Dafydd on Twitter, sign up now for email updates from this blog or subscribe to the feed.

6 comments
Comment by Ed posted on
Will this apply to mod.uk alongside gov.uk?
Comment by Dafydd Vaughan posted on
Hi Ed,
At the moment, this will only apply to services running on `service.gov.uk` domains.
Regards,
Dafydd
Comment by Paul posted on
So, just to clarify, DMARC policy will only apply to @*.service.gov.uk domains? This will not be implemented for @*.gsi.gov.uk?
Comment by Rosalie Marshall posted on
Not at the moment, Paul.
service.gov.uk will be the only domain affected by these updates.
Comment by Nick Woodcraft posted on
The changes described here only apply to *.service.gov.uk, but we have separately asked all government organisations to use DMARC as part of our secure email guidance:
https://www.gov.uk/guidance/common-technology-services-cts-secure-email-blueprint
We know it'll be harder to get those domains to 'p=reject' so there isn't yet a deadline as there is for service.gov.uk.
Comment by collier van cleef trefle copie posted on
where does all the hardware stuff go? and how do you charge it ahahah. maybe it runs off from the heat of our bodies
collier van cleef trefle copie http://www.vcaalhambra.cn/fr/cheap-vintage-alhambra-necklace-10-motifs-yellow-gold-vcara42800-p220/